Published dossier
The End of Static AI Governance: Why Continuous Oversight Is the New Compliance
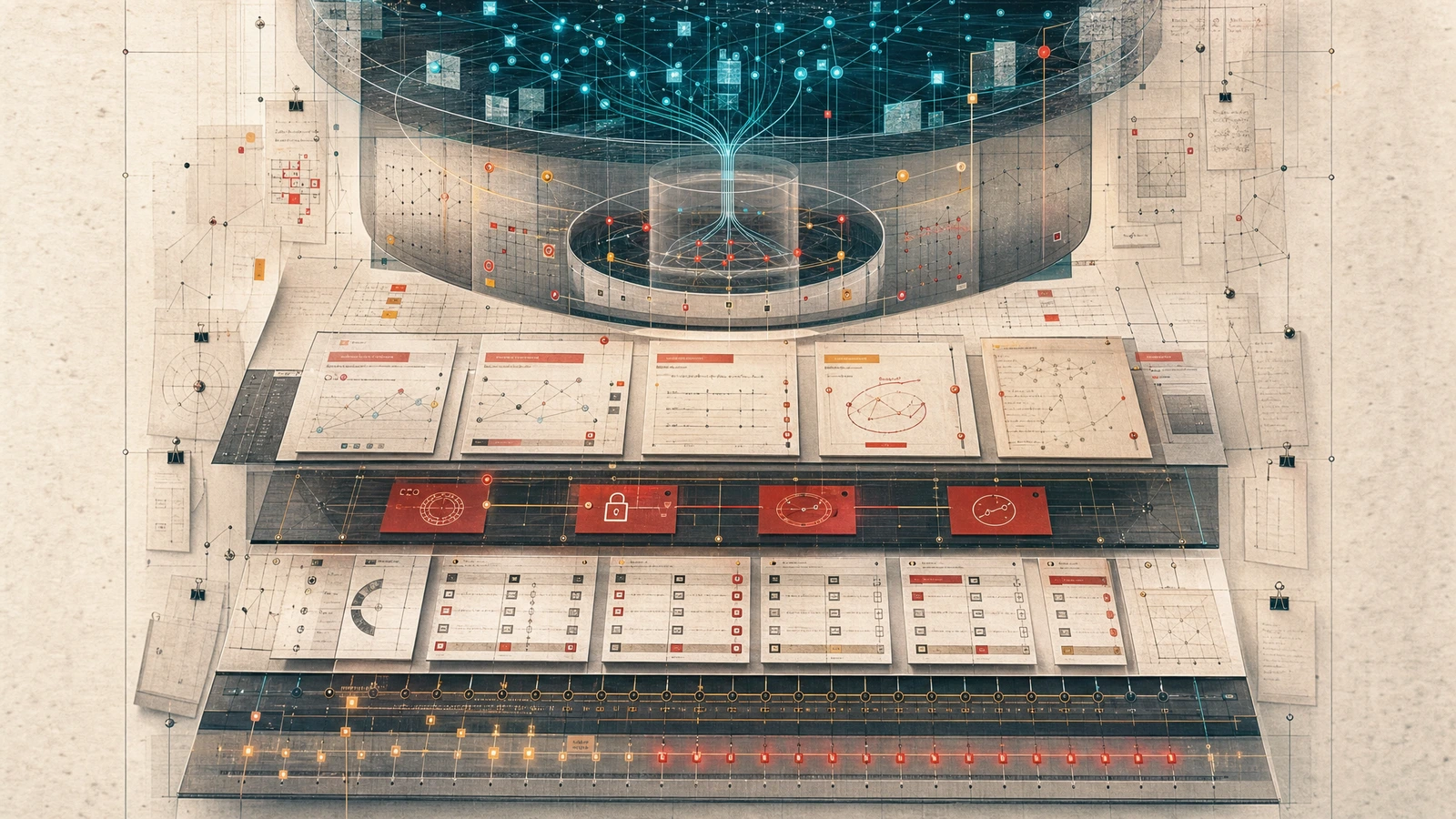
Static compliance frameworks cannot answer real-time model drift or autonomous agent decisions. Governance must be embedded in infrastructure itself—continuous monitoring as regulatory minimum, interoperability through shared standards, real-time anomaly detection for both drift and adversarial patterns.
Board questions changed in 2026. Every board pushes for AI adoption, but the inquiries have evolved from “What’s our AI strategy?” to “How are we securing AI? What’s our AI risk exposure?” This shift signals that governance is no longer a compliance checkbox—it has become a C-suite priority requiring real answers.
Now boards face a new reality: model drift makes periodic audits obsolete, while autonomous agents operate at machine speed. Static compliance frameworks cannot answer either trend.

The Drift Crisis
Harvard Medical School/MIT research published in Nature Scientific Reports documents that 91% of machine learning models show measurable degradation over time—not from bugs or bad data, but because the world changes while models stand still. This is AI aging: a phenomenon that turns monitoring into a governance problem, not just an MLOps task. NIST’s 2025 AI risk-management profile specifically requires real-time continuous monitoring and anomaly detection as a response to this reality.
When your model drifts continuously, governance cannot be an annual exercise or quarterly review. It must be embedded in infrastructure itself.
The Agent Imperative
AI agents are redefining how organizations approach oversight. PwC’s 2025 Responsible AI Survey found that a majority of leaders expect AI agents to reshape governance within the next year, adapting their frameworks to consider fully autonomous systems and embedding testing, data access controls, and telemetry directly into design rather than reacting to risks post-deployment.
Agents operate autonomously at machine speed. Governance frameworks designed for human-centric workflows cannot keep pace with autonomous decision-making without fundamental redesign.
The Security Dimension
Governance cannot be siloed from security operations. Glean’s AI governance data shows phishing emails increased 202% in H2 2024, with 82.6% now using AI technology and 78% of people opening AI-generated phishing emails.
This is not a distant threat—it’s current infrastructure risk at scale. The same governance systems that manage model drift must also detect anomalous patterns indicative of adversarial use.
Regulatory Convergence Around Standards
Global regulatory fragmentation is driving convergence around ISO/IEC standards as the interoperability imperative. California’s Transparency in Frontier AI Act (SB53) requires major AI developers to report safety incidents and publish risk management framework information, as summarized in MoFo’s SB53 analysis. New York’s RAISE Act mandates frontier model developers implement mitigations for critical harm risks, as covered in DLA Piper’s RAISE Act overview.
The EU Code of Practice for general-purpose AI models, effective August 2025, serves as a bridge before formal standards availability. ISO/IEC 23894:2023 and ISO/IEC 42001:2023 are being leveraged across jurisdictions to drive interoperability among domestic AI policy. For organizations facing the August enforcement cliff, these standards provide a roadmap for compliance before enforcement activates.
Governance-as-Infrastructure
The new paradigm requires treating governance as infrastructure rather than audit documentation:
- Embed controls at design time, not post-deployment
- Continuous monitoring as regulatory minimum under NIST’s 2025 profile
- Interoperability through shared standards such as ISO/IEC 23894:2023
- Real-time anomaly detection for both drift and adversarial patterns
This infrastructure approach addresses the same visibility problem explored in the multi-tool governance gap: when multiple agents operate across different surfaces, governance must be structural rather than retrospective.
Implementation Imperatives
Organizations embedding controls at design time will outpace those reacting post-deployment. The practical requirements include:
- Event logging across the AI lifecycle - capturing commit metadata, agent identity, prompt context hashes, and review gate decisions with rationale under shared standards such as ISO/IEC 42001:2023
- Testing + telemetry + data controls as baseline capabilities - continuous monitoring that operates at agent speed
- Audit trails connecting AI interactions back to executive accountability - evidence that survives regulatory scrutiny
For AI coding specifically, spec-driven development workflows operationalize this by making specifications the source of truth and focused context for AI agents, with review evidence and audit decisions becoming governed artifacts before and during agentic work. This connects directly to why context engineering is the missing governance layer - governance must happen upstream at the context layer, not after code generation.
What To Do Now
Three questions help leaders assess readiness:
- Can you trace model drift to continuous monitoring? If your governance is periodic rather than continuous, you cannot answer real-time degradation questions.
- Do your controls operate at agent speed? Human-in-the-loop review cannot keep pace with autonomous agents without structural redesign.
- Is your audit trail evidence-based or policy-based? Templates and form-filling do not satisfy regulatory requirements for high-risk systems.
The Path Forward
Winners in this new paradigm won’t be teams with the most AI tools or highest adoption rates. They will be organizations that treat governance as an integrated system capable of operational enforcement at machine speed, with continuous monitoring and design-time controls making compliance automatic rather than retrospective.
The drift crisis is here. The agent transformation is underway. Regulatory convergence around standards continues. The question is whether your organization can transition from periodic audit to continuous infrastructure before the next incident forces your hand.